Threat Detection in Hybrid Cloud Resource Allocation
Hybrid cloud setups are powerful but introduce unique security risks. With workloads constantly moving across on-premises, private, and public cloud environments, the attack surface shifts rapidly. Misconfigurations during resource scaling, lateral movement risks, and insider threats are the top challenges organizations face. By 2025, 99% of cloud security failures will stem from customer misconfigurations, highlighting the need for proactive measures.
Key Takeaways:
- Misconfigurations: Fast scaling often leads to exposed APIs, open databases, and weak IAM policies.
- Lateral Movement: Attackers exploit gaps between environments, using credentials to bypass detection.
- Insider Threats: High-level permissions in hybrid setups increase risks of misuse and account takeovers.
Solutions:
- Continuous Scanning: Use tools like CSPM and CDR to monitor and fix misconfigurations in real-time.
- Behavioral Analysis: Leverage AI-driven tools like UEBA to detect unusual activity and insider threats.
- Network Traffic Monitoring: Focus on "east-west" traffic to detect lateral movement between workloads.
- Zero Trust Policies: Enforce strict access controls and verify all requests.
- Microsegmentation: Isolate workloads to limit potential damage in case of breaches.
Hybrid cloud security demands a layered approach combining advanced tools, real-time monitoring, and strict access controls to mitigate risks effectively.
Going Beyond the Basics in Azure and Hybrid Cloud Security with Vectra AI
Security Threats in Hybrid Cloud Resource Allocation
Hybrid cloud environments come with their own set of security hurdles, largely due to the dynamic nature of resource allocation. This constant flux creates vulnerabilities that attackers are quick to exploit. Let’s break down some of the most pressing threats.
Misconfigurations in Resource Scaling
The fast-paced scaling of hybrid cloud environments often clashes with traditional security protocols. A single click or a quick code update can launch new resources, but this speed frequently bypasses established change management processes. When teams work across multiple platforms like Amazon VPC, Azure VNet, and Google VPC, misconfigurations are almost inevitable.
These errors can lead to exposed APIs, open databases, storage buckets with overly permissive access, and poorly configured network security groups. What’s worse, security policies designed for on-premises systems don’t always translate seamlessly to public cloud services. This mismatch can leave critical gaps in firewall rules and intrusion detection systems. With 89% of organizations now adopting multicloud strategies, the complexity of managing consistent security settings across platforms has grown exponentially, increasing the risk of errors.
These missteps not only create entry points for attackers but also open the door for lateral exploits, especially during workload transfers.
Lateral Movement Risks During Workload Transfers
The movement of workloads between on-premises and cloud environments presents another layer of risk. As traditional perimeters blur, attackers exploit the "seams" where security controls are inconsistent. These gaps allow them to pivot between systems undetected. Recent cases show attackers using legitimate credentials and short-lived workloads to move laterally, bypassing detection.
Groups like the Rhysida ransomware gang have taken this a step further by embedding themselves into cloud identity systems such as Azure AD. By combining an initial endpoint compromise with persistence in directory services, they can accelerate lateral movement across both IaaS and SaaS platforms. They also disable defenses from within, making their actions appear as normal user behavior. The use of recycled IP addresses and transient workloads complicates continuous monitoring, providing attackers with the cover they need to operate unchecked.
Anomalous Traffic and Insider Threats
Insider threats become even more dangerous in hybrid clouds, where high-level permissions are often required for resource allocation. Malicious insiders can intentionally create insecure configurations that blend into routine operations, leveraging the complexity of these systems. Alarming statistics show account takeover attacks surged by 250% in 2024, enabling attackers to use stolen credentials to mimic legitimate users while stealing data or hijacking resources for activities like cryptocurrency mining or DDoS attacks.
Monitoring insider threats is particularly challenging in hybrid setups. Traditional tools focus on "north-south" traffic – data entering or leaving the network – but hybrid environments demand visibility into "east-west" traffic, which moves between internal workloads and cloud tiers. Shadow IT adds another layer of risk. Developers often spin up workloads using personal accounts to bypass administrative hurdles, creating unmanaged assets with default passwords and hidden vulnerabilities. These rogue resources are prime targets for both external attackers and malicious insiders who know how to exploit these blind spots effectively.
Threat Detection Techniques for Hybrid Cloud Resource Allocation
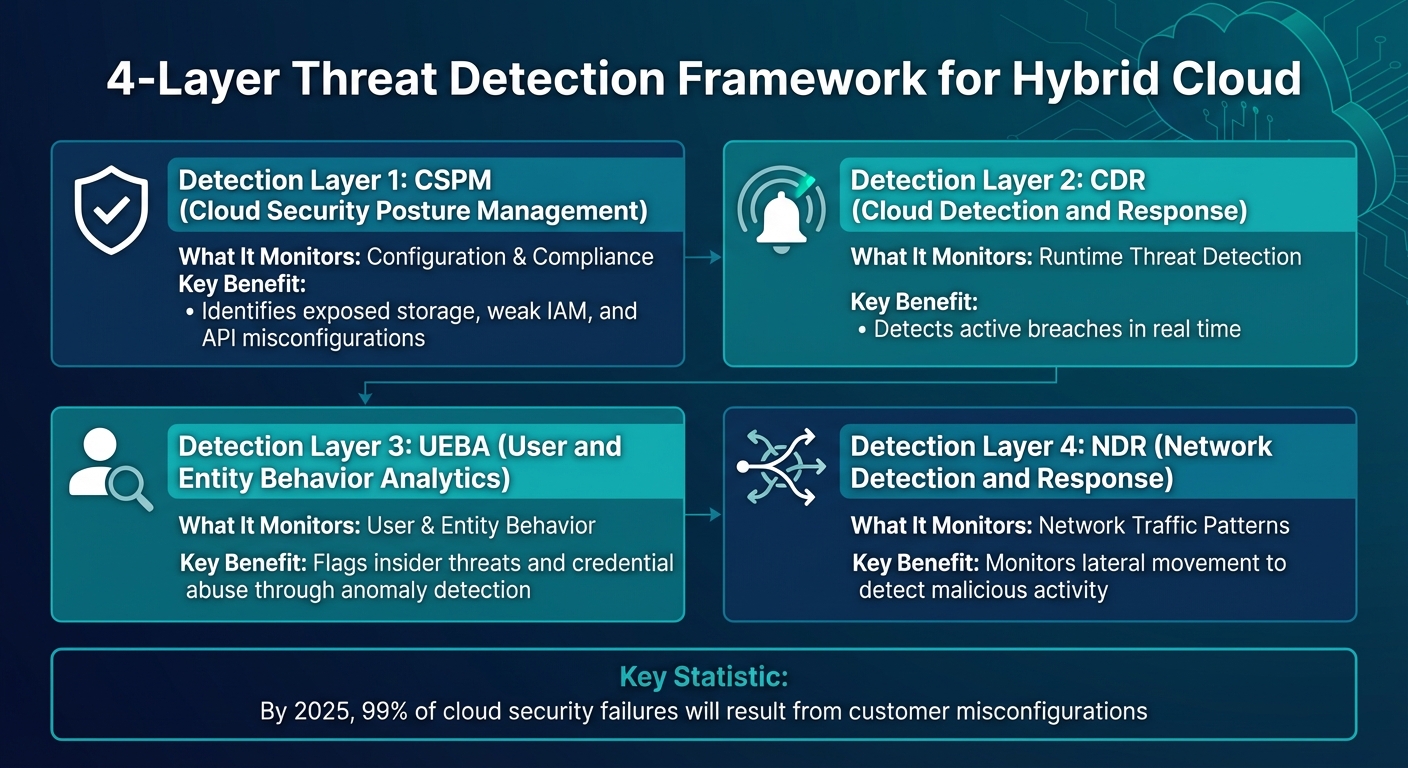
Hybrid Cloud Threat Detection Layers and Security Tools Comparison
As hybrid cloud environments grow increasingly dynamic, detecting and mitigating threats requires a shift from traditional security methods. The fluid nature of resource allocation – where workloads can appear and disappear in seconds – demands tools that can keep up with rapid changes while analyzing massive volumes of data across platforms.
Continuous Vulnerability Scanning
The cornerstone of hybrid cloud security is regular scanning. Tools like Cloud Security Posture Management (CSPM) continuously monitor your cloud assets, identifying misconfigurations, outdated software, and weak access controls before attackers can exploit them. These tools also offer immediate guidance to address issues such as weak IAM policies or exposed APIs.
Here’s a striking statistic: By 2025, 99% of cloud security failures are expected to result from customer misconfigurations. This highlights why continuous scanning is non-negotiable. Modern Cloud Detection and Response (CDR) tools enhance this process by analyzing cloud activity in real time, slashing detection times from the typical 15+ minutes of batched log processing to mere seconds. This speed is critical, as attackers often exploit vulnerabilities within minutes of their discovery.
"Real-time security is the difference between stopping a breach and needing incident response – every second counts. Today’s adversary moves fast and across domains, and defenders can’t afford to waste time waiting for cloud logs to process or detections to populate."
- Elia Zaitsev, Chief Technology Officer, CrowdStrike
Integrating security early in the development cycle, a practice known as shift-left security, further enhances protection. Tools like Trivy and Docker Security Scanning check container images for vulnerabilities during development, while Static Application Security Testing (SAST) identifies code flaws before deployment. These proactive measures help secure resources before they even go live.
Beyond scanning, monitoring subtle behavioral changes adds another layer of defense.
Behavioral Anomaly Detection
While traditional tools focus on known threats, behavioral analysis identifies unusual activities. User and Entity Behavior Analytics (UEBA) leverages AI and machine learning to establish baselines for normal operations across identity, network, and data layers. Deviations, such as a user accessing far more data than usual or logging in from two continents within an hour, are flagged instantly.
This method is particularly effective against insider threats and credential-based attacks, which are leading causes of cloud breaches. For instance, a financial services company with 8,000 employees used Microsoft Entra ID Protection and Sentinel to detect "password spray" attacks – defined as 50+ failed login attempts across 10+ accounts from a single source. By setting analytics rules, they reduced detection time from over 30 days to mere minutes.
Extended Detection and Response (XDR) takes this a step further by correlating behavioral signals across endpoints, email, identity, and cloud infrastructure. For example, a manufacturing company used behavioral analytics to link storage access anomalies with SQL schema changes, quickly identifying an advanced persistent threat (APT).
Effective behavioral monitoring spans multiple layers: compute (to detect resource hijacking like cryptomining), storage (to catch bulk data extractions), and identity (to uncover credential misuse). Without such tools, sophisticated threats can go undetected for over 30 days – a dangerous delay in cloud security.
Network Traffic Monitoring
To complement vulnerability scanning and behavioral analysis, monitoring network traffic provides essential visibility into lateral movement. In hybrid cloud environments, this means focusing not just on "north-south" traffic (data entering or leaving the network) but also on "east-west" traffic – the lateral movement between workloads. Attackers often exploit these pathways after gaining initial access, especially at the intersection of on-premises and cloud systems.
Network Detection and Response (NDR) tools analyze data sources like VPC Flow Logs, DNS logs, and firewall events to detect potential threats. For example, Amazon GuardDuty processes billions of events using machine learning and threat intelligence. However, despite 77% of cybersecurity leaders monitoring east-west traffic, 40% of this data still lacks the context needed for effective threat detection.
Centralized logging is crucial for actionable insights. By streaming network logs to a Security Information and Event Management (SIEM) platform like Microsoft Sentinel, Splunk, or IBM QRadar, organizations can correlate data across their entire hybrid environment. Enabling VPC Flow Logs in AWS or Network Security Group (NSG) Flow Logs in Azure captures metadata about IP traffic, helping establish a baseline for normal network interactions. Deviations from this baseline can signal malicious activity.
A comprehensive approach combines CSPM, CDR, UEBA, and NDR, as summarized below:
| Detection Layer | What It Monitors | Key Benefit |
|---|---|---|
| CSPM | Configuration & Compliance | Identifies exposed storage, weak IAM, and API misconfigurations |
| CDR | Runtime Threat Detection | Detects active breaches in real time |
| UEBA | User & Entity Behavior | Flags insider threats and credential abuse through anomaly detection |
| NDR | Network Traffic Patterns | Monitors lateral movement to detect malicious activity |
Automation is key to effective network monitoring. By scripting thresholds and automating remediation, organizations can ensure the "monitor-detection-action" cycle happens without human intervention. This reduces dwell time – the period attackers remain undetected in your system – and minimizes potential damage.
sbb-itb-59e1987
Best Practices for Securing Hybrid Cloud Resource Allocation
Securing resource allocation in a hybrid cloud setup requires a layered approach to block potential threats. By incorporating multiple defenses, you make it significantly harder for attackers to exploit vulnerabilities during resource allocation.
Implementing Zero Trust Policies
Zero Trust flips the traditional security mindset by treating every request as suspicious until verified. This is especially critical during resource allocation, where workloads are constantly spinning up or scaling across on-premises and cloud environments.
At the heart of Zero Trust is continuous verification. Every access request is checked and rechecked, no matter where it originates. Transitioning from network-based to identity-based security is a key step. Tools like SPIFFE (Secure Production Identity Framework for Everyone) assign consistent identities to services, allowing you to base access policies on the who rather than the where.
Another key element is Just-In-Time (JIT) access, which provides temporary, task-specific permissions only when necessary. For example, developers might receive short-term access to specific resources, minimizing the risk of credential misuse.
To get started, map out all assets in your hybrid cloud and identify who needs access to what and why. Use your cloud security tools to enforce strict "deny by default" policies, ensuring that any unauthorized resource creation is blocked before it becomes a problem. This approach not only minimizes misconfigurations but also lays the groundwork for further isolation strategies.
Microsegmentation for Workload Isolation
Microsegmentation breaks your network into smaller, more manageable zones, down to the level of individual workloads. This ensures that if one segment is compromised, the attacker can’t freely move across your entire environment. This is particularly important during resource allocation, where new workloads might temporarily have elevated privileges or incomplete security measures.
Unlike broader segmentation, microsegmentation focuses on isolating each workload. Each connection between segments requires explicit authentication and authorization, limiting the exposure of sensitive resources.
"Network isolation is no longer optional – it is a necessary control for safeguarding cloud and hybrid environments."
You can enforce microsegmentation using tools like Network Security Groups (NSGs) and Access Control Lists (ACLs), which allow you to apply least-privilege access rules. For example, grouping all components of a single application within one boundary simplifies monitoring and makes it easier to spot anomalies.
Additionally, disable default outbound access for cloud resources. Many come with unrestricted Internet access by default, which can introduce unnecessary risks. By applying strict egress rules, you ensure workloads only communicate with approved destinations.
However, overdoing segmentation can lead to unnecessary complexity.
"Micro-segmentation beyond a reasonable limit loses the benefit of isolation. When you create too many segments, it becomes difficult to identify points of communication."
To address this, automate the management of networking resources to avoid configuration errors that attackers could exploit.
AI-Driven Threat Intelligence
AI-driven threat intelligence processes vast amounts of security data in real time, making it an essential tool for identifying and addressing threats during resource allocation.
With User and Entity Behavior Analytics (UEBA), AI establishes a baseline for normal activity and flags unusual behavior. For example, if a service account starts acting unpredictably during a resource scaling operation, UEBA can detect and alert you to the anomaly.
AI also enables automated remediation, which can quickly fix insecure configurations before they become exploitable. This is especially critical because the dynamic nature of cloud environments often introduces threats that manual monitoring might miss.
Centralized logging is another key component. By aggregating logs from both on-premises and cloud environments, AI can correlate data to identify cross-environment threats. For instance, if an on-premises server is compromised and the attacker uses those credentials to allocate cloud resources, a unified logging system can help connect the dots.
Finally, adaptive network hardening uses AI to analyze traffic patterns and recommend stricter security policies. This creates a feedback loop that continuously strengthens your defenses, reducing the time attackers can linger in your environment.
Serverion‘s Security Features for Hybrid Cloud Deployments
Serverion pairs proactive threat detection with advanced security measures, ensuring hybrid cloud deployments remain secure during resource allocation.
DDoS Protection and Data Security
Serverion’s Ultimate DDoS Protection can handle attacks up to 4 Tbps, keeping operations running smoothly even during scaling or workload transfers. To safeguard data, all stored information is encrypted, and the system receives regular security updates. Multi-layered hardware and software firewalls add another layer of defense. This is especially critical during resource allocation, as new workloads might come with elevated privileges or temporary security settings.
Managed Services for Threat Monitoring
Serverion offers 24/7 network monitoring, combining automated systems with on-site experts to quickly address unusual traffic or access issues during resource scaling. With a 99.9% uptime guarantee, their monitoring ensures reliability.
Their managed services cover server administration for both Windows and Linux, including tasks like OS updates, patching, and configuration hardening. To prevent data loss during resource transitions, automated backups and snapshots are performed multiple times daily, allowing for quick recovery if a threat arises. These services integrate seamlessly with Serverion’s scalable hosting, providing continuous protection at every phase of deployment.
Scalable Hosting Solutions for Hybrid Environments
With 37 data center locations worldwide, including Amsterdam, New York, and The Hague, Serverion enables you to deploy Virtual Private Servers (VPS) or dedicated servers close to your existing infrastructure. This setup reduces latency while maintaining consistent security during resource allocation. VPS plans range from $11/month (1 core, 2 GB RAM, 50 GB SSD) to $220/month (12 cores, 64 GB RAM, 1,000 GB SSD, 100 TB bandwidth).
Serverion offers both managed and unmanaged hosting options, giving you flexibility in choosing the level of oversight that suits your needs. For demanding tasks like Big Data processing or blockchain hosting, their specialized infrastructure supports resource-heavy operations without compromising security. With full root access on VPS instances and professional management services, you can customize security configurations while relying on robust baseline protections.
Conclusion
As outlined earlier, hybrid cloud environments bring unique challenges that require flexible and well-coordinated security measures. The way resources are allocated in these setups introduces risks like misconfigurations, lateral movement, and identity-based attacks. These vulnerabilities often go unnoticed for weeks, giving attackers ample time to escalate privileges and steal sensitive data.
To address these issues, organizations should focus on centralizing security data through unified logging, behavioral analytics, and advanced monitoring powered by AI. This approach can drastically cut down detection times – from weeks to mere minutes. Implementing extended detection and response (XDR) systems helps connect the dots across endpoints, identity systems, and infrastructure. Additionally, adopting Zero Trust principles, microsegmentation, and automated remediation processes ensures a stronger defense against potential threats. It’s also critical to understand the shared responsibility model: cloud providers secure the infrastructure, but it’s up to the customers to safeguard their applications, data, and configurations.
Key Takeaways
- Centralize security data and use behavioral analytics: Combine logs from identity, network, and application layers into a single security information and event management (SIEM) platform. Track changes in management planes, authentication patterns, traffic flows, and data operations. Leverage AI and machine learning to spot anomalies, such as unusual login locations or spikes in data transfers. Pay close attention to identity-related activities like authentication and privilege escalation, as these are common attack vectors. Automated remediation tools are vital to quickly fix misconfigurations before they can be exploited.
- Unify security controls across environments: Standardize security practices for both on-premises and cloud-based systems. Use microsegmentation to monitor traffic between subnet boundaries and detect lateral movement during workload transitions. Start threat modeling early in the design process with frameworks like the "4 Question Frame" to proactively address vulnerabilities before deployment. By integrating these strategies, hybrid cloud environments can be both secure and flexible, ensuring that security measures keep pace with the demands of modern cloud operations.
FAQs
What are the main security challenges in hybrid cloud environments?
Hybrid cloud environments blend on-premises infrastructure with public cloud services, but this setup introduces unique security hurdles. As data moves between these environments, the risks of data breaches and leaks grow, especially if encryption methods and transfer protocols aren’t aligned. On top of that, differences in security tools and policies across the hybrid setup can lead to misconfigurations and policy drift, leaving critical resources exposed.
Another significant challenge is visibility gaps. Monitoring tools often struggle to provide a unified view of on-premises and cloud systems, making it harder to identify and respond to threats. This lack of visibility can expose insecure APIs and integration points, which attackers might exploit. Managing credentials across these environments adds another layer of complexity, increasing the chances of privileged access risks. Furthermore, compliance requirements become more difficult to meet when data crosses regional or national boundaries.
To mitigate these risks, organizations should implement unified security policies, ensure end-to-end encryption, centralize logging, and automate configuration checks. Serverion’s managed hybrid cloud solutions simplify securing hybrid architectures by offering integrated monitoring, consistent policy enforcement, and secure API gateways – helping organizations maintain both performance and security.
How can organizations monitor and stop lateral movement in hybrid cloud environments?
To keep lateral movement in hybrid cloud environments in check, adopting a Zero Trust approach is essential. This strategy treats every user, workload, and network segment as untrusted until thoroughly verified. By implementing micro-segmentation and enforcing strict identity-based access controls, organizations can limit resource access and block attackers from moving freely across systems. Pair this with least-privilege policies and continuous identity validation to counter threats like credential theft or token misuse.
Boosting visibility is another critical step. Collect and analyze logs, telemetry, and behavioral data from cloud APIs, on-premise systems, and virtual networks. Centralizing this data in a security platform allows for quick detection of unusual activity, such as privilege escalation or suspicious traffic patterns, enabling a faster response.
Lastly, a defense-in-depth strategy is vital. This involves combining network segmentation, intrusion detection, and automated policy enforcement. Regular threat modeling, maintaining an up-to-date asset inventory, and having a unified incident response plan in place can significantly reduce risks. These measures ensure lateral movement is identified and stopped before it threatens critical workloads.
How does AI improve threat detection in hybrid cloud environments?
AI is transforming threat detection in hybrid cloud environments by utilizing machine learning and deep learning to sift through massive datasets from both public and private cloud systems. These advanced technologies pinpoint potential risks early, stopping them before they evolve into full-blown attacks.
With real-time analysis, AI automates the identification of intricate and ever-changing threat patterns, boosting the speed and precision of security measures. This hands-off, proactive strategy allows organizations to protect their hybrid cloud setups from advanced cyber threats while reducing the need for constant manual oversight.







