Cloud Storage Permissions: Best Practices
Cloud storage permissions are the backbone of data security. They control who can access files, what actions they can take, and how data is shared. Misconfigured permissions can lead to data breaches, compliance violations, and financial losses. This guide breaks down the essentials for managing permissions effectively, including:
- Least Privilege Principle (PoLP): Give users only the access they need.
- Access Models: Choose between Role-Based (RBAC) for simplicity or Attribute-Based (ABAC) for dynamic control.
- Multi-Factor Authentication (MFA): Add extra layers of security.
- Regular Audits: Identify unused or excessive permissions and fix vulnerabilities.
- Automation Tools: Simplify permission management at scale.
The goal? Protect data, ensure compliance, and maintain operational efficiency. Let’s explore how to implement these strategies step-by-step.
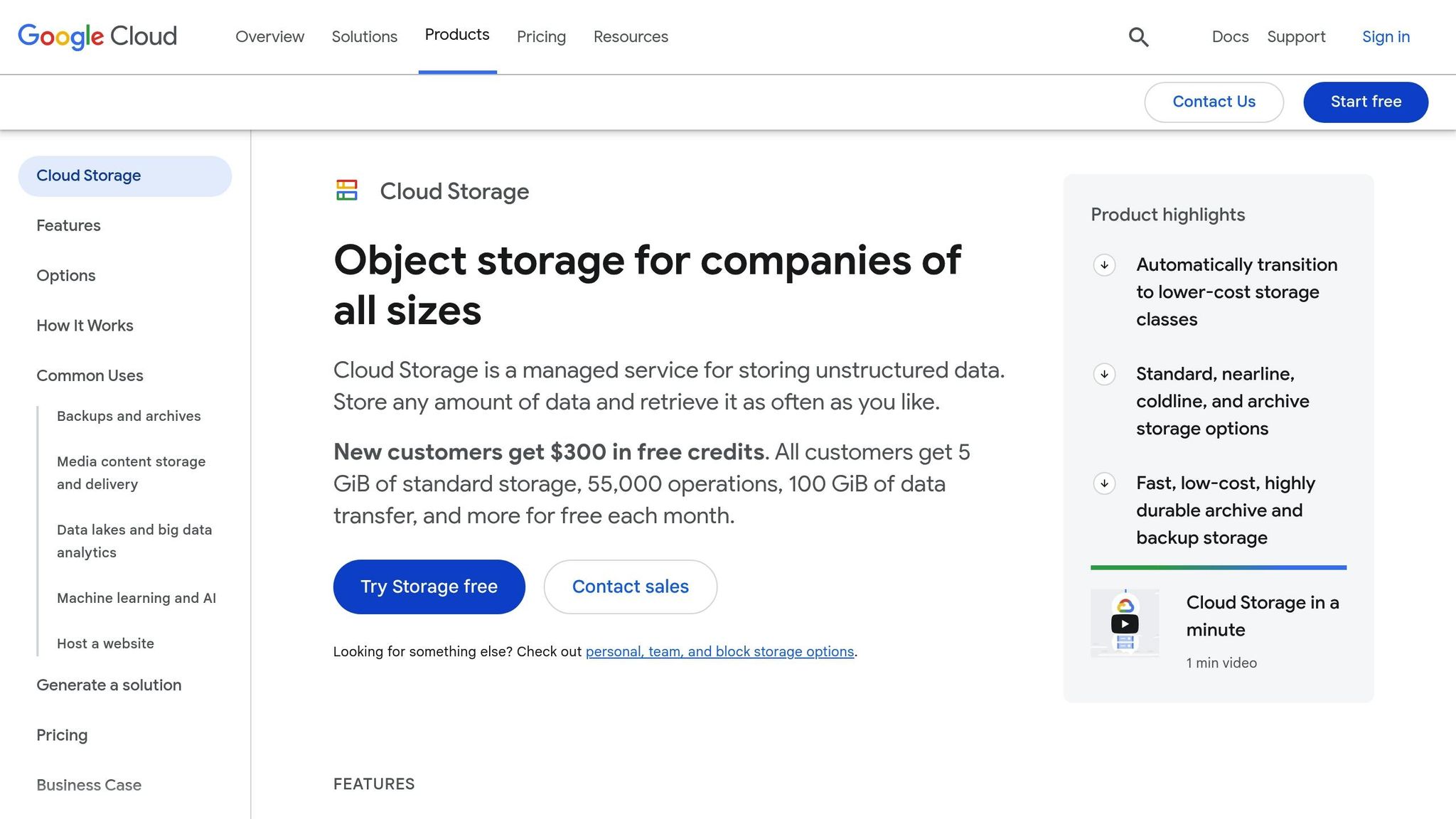
[GCP] SECURING Google Cloud STORAGE BUCKETS with Terraform
Core Principles of Permission Management
Keeping cloud storage secure means sticking to proven security principles. These concepts act as the backbone of any strong permission strategy, layering protections to keep your data safe.
Principle of Least Privilege (PoLP)
The Principle of Least Privilege is the foundation of effective permission management. It’s all about granting users just enough access to do their jobs – no more, no less.
Think of it like handing out keys: you wouldn’t give someone access to every room in a building if they only need one. For example, a marketing coordinator might need to view campaign assets but shouldn’t be able to delete financial records or tweak system settings.
This principle helps reduce your attack surface. If a user account gets compromised, the potential damage is limited to what that account can access.
It also lowers internal security risks by reducing the chances of accidental or intentional misuse. Regularly reviewing access as roles and responsibilities change ensures permissions stay aligned with the least privilege principle.
Role-Based Access Control (RBAC) vs. Attribute-Based Access Control (ABAC)
To put PoLP into practice, you’ll need the right access control model. Two common options are Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC). Choosing the right one can simplify your system or, if misapplied, create headaches.
- RBAC groups permissions into predefined roles like "Marketing Manager", "Financial Analyst", or "IT Administrator." Users inherit permissions based on their assigned role. This system works well for organizations with clear hierarchies and stable job functions.
- ABAC uses a more dynamic setup, deciding access based on multiple attributes like user characteristics, resource details, and environmental factors. For instance, ABAC might consider the time of day, location, or the type of device being used to determine access.
| Aspect | RBAC | ABAC |
|---|---|---|
| Complexity | Simple and straightforward | More complex but highly adaptable |
| Best for | Stable organizations with clear roles | Environments with changing access needs |
| Scalability | Can become hard to manage with too many roles | Handles complexity more effectively |
| Maintenance | Easier to maintain in stable setups | Requires ongoing policy adjustments |
| Granularity | Limited to role-based permissions | Offers fine-tuned, context-aware control |
Most organizations start with RBAC because it’s easier to set up. Over time, as needs grow, some transition to ABAC or adopt a hybrid model – using RBAC for general access and ABAC for sensitive resources that demand more nuanced controls.
Multi-Factor Authentication and Password Policies
No matter how well you manage permissions, weak user accounts can still create vulnerabilities. That’s where Multi-Factor Authentication (MFA) and strong password policies come into play.
MFA adds extra layers of security by requiring users to verify their identity in multiple ways: something they know (like a password), something they have (a phone app or hardware token), and sometimes something they are (biometric data). Even if a password is compromised, MFA can block unauthorized access.
Two-factor authentication alone can stop many automated attacks. For cloud storage with sensitive data, MFA should be non-negotiable – especially for accounts with higher-level permissions.
Password policies complement MFA by ensuring accounts are harder to breach. Encourage passwords that are long enough to resist brute-force attacks but still practical for users. A 15-character passphrase, for example, often provides better security and usability than an 8-character password full of special symbols.
For added protection, consider adaptive authentication. This approach adjusts security requirements based on risk. For example, users logging in from familiar devices and locations might face standard checks, while unusual activity triggers extra verification steps. This balances security with convenience.
Skip frequent mandatory password changes unless there’s a clear reason, like a suspected breach. Instead, focus on detecting compromised credentials and encourage users to update passwords only when necessary. This avoids the frustration and bad habits that frequent changes can cause while keeping accounts secure.
Setting Up and Managing Permissions
Getting your permissions right from the beginning is key to keeping your data safe and avoiding headaches down the road. By applying solid security principles early on, you’ll save time, reduce troubleshooting, and ensure your system stays secure. Make use of reliable IAM tools and well-defined policies to turn these principles into everyday practices.
Using Identity and Access Management (IAM) Tools
Identity and Access Management (IAM) tools are the backbone of managing permissions in cloud storage. They help you set up users, assign roles, and control access across your cloud environment. By centralizing these tasks, IAM tools help you avoid errors and maintain consistent security protocols.
Cloud providers offer a wide range of IAM permissions, but managing them carefully is crucial. Create specialized service accounts with limited, task-specific permissions and align user accounts with their actual job roles. This approach minimizes the risk of granting unnecessary access, helping you maintain tighter control over your environment.
Best Practices for Organizational Policies
Set up strict access controls tailored to each job role, and make it a habit to review permissions regularly. These reviews help you stick to the least privilege principle, preventing over-permissioning and reducing security risks.
Granular Access Control Tools
Take advantage of tools like ACLs to manage file-level permissions and use context-aware IAM conditions to control access based on factors like time, location, or device. These detailed controls ensure that permissions are always in line with your operational and security requirements.
Monitoring and Auditing Permissions
Setting up permissions is just the first step. To keep your cloud storage secure over time, continuous monitoring and regular audits are essential. Without consistent oversight, permissions can drift, leaving your systems vulnerable. By implementing detailed logging and review processes, you can stay ahead of potential security issues.
Auditing Permissions and Detecting Misconfigurations
Permission auditing is all about ensuring access remains necessary and appropriate. Look for accounts with excessive or unused privileges. For example, service accounts often accumulate permissions over time, and user accounts might retain access to resources they no longer need.
Automated tools like Cloud Security Posture Management (CSPM) solutions and scanners can identify issues such as public storage buckets, overprivileged accounts, and dormant users. These tools can also check for compliance violations against standards like SOC 2 or GDPR.
Start your audits by focusing on high-risk areas. Pay close attention to accounts with write access to sensitive data, users who can modify IAM policies, and service accounts with permissions to create or delete resources. Don’t overlook cross-account permissions and external sharing settings – these are common weak points in cloud security.
Logging and Audit Trails
When anomalies arise, logs become your best resource for investigation. Log every permission change, including role assignments, policy updates, and access grants. These records are critical during security incidents, compliance audits, and forensic investigations.
Maintain audit trails that document all access attempts. Store these logs in a centralized location with clearly defined retention policies. Many compliance frameworks require logs to be kept for specific durations, often ranging from one to seven years.
Set up real-time alerts for changes to permissions. For instance, if someone grants administrative access to a new user or alters security policies, your security team should be notified immediately. These alerts enable you to catch unauthorized actions before they escalate.
Use log analysis tools to identify trends in permission usage. These tools can highlight unused permissions, which may indicate opportunities to tighten access controls. They can also flag unusual activity, such as permissions being used in unexpected ways, which could signal a compromised account or insider threat.
Regular Permission Reviews
Regular reviews help enforce the Principle of Least Privilege. Scheduled permission reviews should be conducted periodically – quarterly reviews are sufficient for most organizations, but high-security environments may require monthly checks. During these reviews, ensure that user permissions align with their current job responsibilities and that service accounts haven’t accumulated unnecessary privileges.
Thorough documentation is key to effective reviews. Keep records of why specific permissions were granted, when they were last reviewed, and who approved them. This transparency helps reviewers make informed decisions about whether to keep, adjust, or remove permissions during audits.
Establish permission review workflows that involve the right stakeholders. Resource owners should confirm that access to their systems is still appropriate, while managers should verify that their team members need their current access levels. While automated tools can flag unused permissions, manual validation is essential to ensure changes are accurate and contextually appropriate.
sbb-itb-59e1987
Overcoming Permission Management Challenges
Managing cloud storage permissions can feel like navigating a maze. For many organizations, keeping access secure and organized is a constant battle. But understanding the hurdles and having practical strategies can mean the difference between a well-secured system and a potential security nightmare.
Common Permission Management Challenges
One of the biggest headaches is permission sprawl. As teams expand and projects pile up, access rights tend to snowball. Over time, users and service accounts often end up with more permissions than they need. The result? A tangled mess of access rights that’s nearly impossible to sort out manually.
Then there’s shadow access, which happens when users gain unintended access through indirect means – like being added to a group they shouldn’t be in or inheriting permissions through nested roles. These hidden pathways can easily slip through the cracks during routine reviews, leaving behind significant security gaps.
For larger organizations, scaling permissions becomes a monumental challenge. A system that works for a small team of 50 can completely fall apart when applied to a workforce of 5,000. Manual processes quickly grow unmanageable, leading to mistakes and forcing companies to choose between security and efficiency – a choice no one wants to make.
Another issue is cross-platform complexity. With multiple cloud providers and on-premises systems, each operating with its own permission model, maintaining consistent policies across platforms like Amazon S3, Microsoft Azure, Google Cloud, and internal servers becomes a Herculean task. It requires deep expertise and constant vigilance.
Finally, compliance requirements from regulations like GDPR, HIPAA, and SOX add another layer of complexity. These standards demand strict controls and detailed audit trails, making it critical to balance compliance with operational needs.
Now, let’s explore how automation and other tools can simplify these challenges.
Solutions for Better Permission Management
Automation is a game-changer when it comes to handling permissions at scale. Automated systems can take care of routine tasks like granting, adjusting, or revoking access when employees join, change roles, or leave. This eliminates delays and reduces errors by following predefined rules.
Using permission templates can also streamline the process. Instead of setting up permissions for each user individually, you can create templates for common roles like "Marketing Analyst" or "DevOps Engineer." This ensures consistency and prevents over-permissioning when onboarding new team members.
Centralized management tools are another must-have. They provide a unified view of permissions across all systems, making it easier to spot excessive access or inconsistencies. These tools also allow bulk updates, so you can adjust permissions for entire groups with just a few clicks.
Implementing just-in-time access is a smart way to cut down on standing permissions. With this approach, users request temporary access to specific resources, which is granted through an automated workflow and expires after a set time. This minimizes the attack surface while keeping operations running smoothly.
Permission analytics tools are invaluable for identifying unnecessary or excessive permissions. By analyzing usage patterns, these tools can highlight unused access rights, over-privileged accounts, and unusual activity. This makes it easier to clean up permissions without disrupting workflows.
Finally, integrating with HR systems ensures that permissions stay up-to-date with organizational changes. When someone gets promoted, switches teams, or leaves the company, their access rights can be adjusted automatically, reducing the risk of former employees retaining access to sensitive systems.
To reinforce these strategies, a strong backup and recovery plan is essential.
Backup and Recovery for Permissions
A solid backup and recovery plan acts as your safety net, ensuring your permission structure can bounce back from unintended changes.
Version control for permissions is a lifesaver when something goes wrong. Many cloud platforms keep a history of permission changes, allowing you to see what was modified and when. If needed, you can quickly roll back to a previous state.
Configuration snapshots are another effective tool. Before making major changes to your access controls, take a snapshot of your current setup. If something doesn’t go as planned, you can restore the system to its earlier state. This is especially helpful during system migrations or organizational restructuring.
It’s also critical to have well-documented recovery procedures, and these should be tested regularly. Make sure your team knows how to restore permissions quickly and accurately – because the middle of a security incident is the worst time to discover your backup plan doesn’t work.
Staged rollbacks are a more cautious approach to undoing changes. Instead of reversing everything at once, you can roll back specific parts of the system while keeping others intact. This minimizes disruption and gives you time to pinpoint the root cause of the issue.
Finally, monitoring during recovery is essential to ensure everything is functioning as it should. After rolling back changes, keep an eye on system logs and user feedback to confirm that legitimate access has been restored without introducing new vulnerabilities.
Key Takeaways for Secure Cloud Storage Permissions
Securing cloud storage permissions is about creating a reliable framework that safeguards your organization’s critical assets while ensuring smooth operations. The strategies outlined here work together to build a security system that grows with your business needs.
Summary of Best Practices
- Apply the least privilege principle: Limit user access to only what’s absolutely necessary. This reduces your exposure to potential threats. While it requires ongoing management, the added security is worth the effort.
- Adopt role-based controls: Simplify access management by assigning standardized roles instead of managing individual permissions. This approach aligns access with real-world job functions.
- Automate and audit permissions: Use tools to flag unusual access patterns, identify unused permissions, and ensure policies are consistently enforced. Regular audits help catch and fix potential vulnerabilities.
- Use multi-factor authentication (MFA) and strong passwords: These extra layers of security can block unauthorized access, even if credentials are compromised.
- Maintain robust backup and recovery plans: Document and test procedures for restoring permission configurations after changes or incidents. This preparation minimizes downtime and confusion during emergencies.
These practices can be effectively implemented with the right tools and hosting solutions, ensuring both security and efficiency.
Implementing Secure Permissions with Serverion
Serverion’s infrastructure is designed to support these best practices, offering flexibility and robust security features that align with your organization’s needs:
- Dedicated servers starting at $75/month give you full administrative control. This allows for custom permission configurations tailored to your specific security requirements.
- VPS hosting offers scalable solutions with full root access, enabling seamless deployment of role-based access controls across various virtual environments.
- Global data center locations help meet compliance requirements, allowing you to choose where your data is stored to adhere to regulations like GDPR. Plus, built-in DDoS protection and security monitoring provide extra layers of defense.
- 24/7 expert support ensures help is always available. Whether troubleshooting access issues or implementing complex permission structures, quick assistance can prevent minor issues from escalating into major problems.
- Affordable SSL certificates starting at $8/year make encrypting data in transit straightforward, complementing your broader security strategy. Additionally, Serverion’s server management services can handle the technical side of implementing these best practices, freeing your team to focus on policy and compliance.
FAQs
How does the Principle of Least Privilege (PoLP) help protect cloud storage from data breaches?
Principle of Least Privilege (PoLP)
The Principle of Least Privilege (PoLP) plays a key role in strengthening cloud storage security. It works by ensuring that users and systems only have access to the data and resources they need to perform their specific tasks – nothing more. By keeping permissions tightly controlled, PoLP helps reduce the chances of unauthorized access while also limiting the damage that could result from malicious actions or accidental mistakes.
This approach also shrinks the attack surface, making it more difficult for cybercriminals to exploit potential vulnerabilities. On top of that, it helps prevent accidental data leaks, ensuring sensitive information stays accessible only to those who genuinely require it. Adopting PoLP is a vital step in creating a secure and well-organized cloud environment.
What’s the difference between Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC), and how can I choose the right one for my organization?
The main difference between Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC) lies in how they manage and assign access permissions.
RBAC organizes permissions around predefined roles, such as "Manager" or "HR Team." It’s straightforward to set up and works well for organizations with clear hierarchies and predictable access needs. For example, a manager might automatically gain access to reports and team schedules simply by being assigned the "Manager" role.
On the other hand, ABAC takes a more dynamic approach by using a variety of attributes – like user roles, resource types, or even conditions such as the time of day or location. This flexibility makes it suitable for larger or more complex organizations where access requirements can vary widely. For instance, ABAC could allow a user to access a file only during business hours or from a specific device.
When deciding between the two, think about your organization’s size, structure, and access needs. RBAC is a great option for smaller teams or businesses with stable access patterns, while ABAC is better suited for environments that demand adaptability and scalability.
Why should you regularly audit cloud storage permissions, and how can you do it effectively?
Why Regular Cloud Storage Permission Audits Matter
Regularly auditing cloud storage permissions is a key step in safeguarding sensitive data, staying aligned with security policies, and blocking unauthorized access. These audits help uncover potential weaknesses and ensure that the right individuals have access to the right information.
To carry out a successful audit, begin by clearly defining its scope – decide which systems and permissions need to be reviewed. Then, dive into user permissions to confirm they match specific roles and responsibilities. Look out for any files or folders that might have been unintentionally made public. Additionally, double-check that encryption and backup settings are properly configured to meet security standards. By making audits a routine practice, you not only tighten your security defenses but also stay compliant with industry regulations and recommended practices.







