How Quantum-Resistant Encryption Protects Enterprise Data
Quantum computers are no longer theoretical – they’re advancing fast, with a 31% chance of a cryptographically relevant quantum computer by 2033. This poses a serious threat to encryption methods like RSA and ECC, which could be broken in hours using quantum algorithms. Businesses must act now to safeguard sensitive data, as cyber attackers are already intercepting encrypted information to decrypt later when quantum tech matures.
Here’s what you need to know:
- Why It Matters: Quantum computers can break widely used encryption methods, risking data like financial transactions, healthcare records, and trade secrets.
- Immediate Threat: The "Harvest-Now, Decrypt-Later" strategy means data intercepted today may be vulnerable in the future.
- Solutions: Transition to NIST-approved post-quantum algorithms (ML-KEM, ML-DSA) and upgrade systems to handle larger keys.
- Action Plan: Start with a cryptographic inventory, migrate to quantum-resistant methods, and test systems for performance impacts.
Delaying these steps could leave your enterprise exposed. Protecting data now ensures compliance with future regulations and maintains long-term security.
Quantum Computing Will Break Encryption: Here’s How to Prepare
sbb-itb-59e1987
How Quantum Computers Break Traditional Encryption
Quantum Threats to Encryption: Algorithm Vulnerabilities and Impact Comparison
Shor’s and Grover’s Algorithms Explained
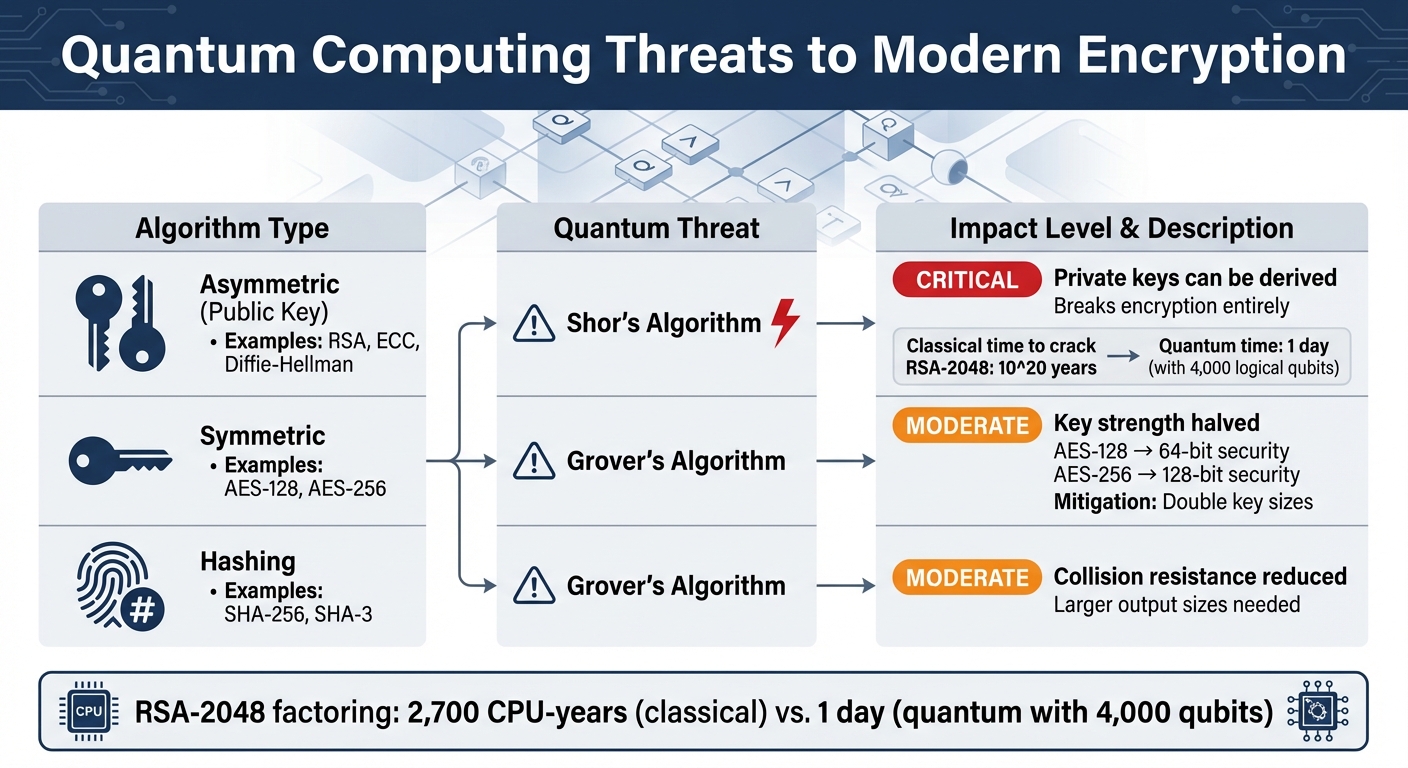
Encryption relies on solving problems that are easy to compute but incredibly tough to reverse. Take RSA encryption, for example – it’s based on multiplying large prime numbers. While multiplying is quick, reversing the process (factoring) is so computationally intense it could take around 10^20 years to crack a 2048-bit key using classical computers.
Shor’s Algorithm changes everything. Quantum computers running this algorithm can factorize large numbers or solve discrete logarithms in polynomial time. What used to take billions of years can now be done in hours or days. For example, factoring an 829-bit RSA number with classical methods required about 2,700 CPU-years. A quantum computer with 4,000 logical qubits could break RSA-2048 encryption in just one day. This makes RSA, ECC, and Diffie-Hellman completely insecure, jeopardizing secure communications, digital signatures, and key exchanges.
Grover’s Algorithm, on the other hand, doesn’t outright break encryption but speeds up brute-force attacks. It reduces the effective strength of symmetric encryption keys by half. For instance, AES-128 would offer only 64-bit security, and AES-256 would drop to 128-bit. While this doesn’t render symmetric encryption useless, it does mean doubling key sizes to maintain current security levels.
| Algorithm Type | Examples | Quantum Threat | Impact |
|---|---|---|---|
| Asymmetric (Public Key) | RSA, ECC, Diffie-Hellman | Shor’s Algorithm | Critical: Private keys can be derived, breaking encryption entirely |
| Symmetric | AES-128, AES-256 | Grover’s Algorithm | Moderate: Key strength halved; doubling key sizes mitigates risk |
| Hashing | SHA-256, SHA-3 | Grover’s Algorithm | Moderate: Collision resistance reduced; larger output sizes needed |
These vulnerabilities highlight the urgent need for quantum-resistant encryption to protect sensitive data. Attackers are already exploiting these weaknesses with new tactics like harvesting encrypted data now for future decryption.
The ‘Harvest-Now-Decrypt-Later’ Threat
Quantum vulnerabilities aren’t just theoretical – adversaries are actively preparing for a quantum future. The Harvest-Now-Decrypt-Later (HNDL) strategy involves collecting encrypted data today, knowing it can be decrypted once quantum computers become powerful enough.
There are real-world examples of this tactic in action. In 2020, data from companies like Google, Amazon, and Facebook was rerouted through Russian servers during a BGP hijacking incident. Experts believe such events are part of large-scale data harvesting operations. Similar cases include Canadian internet traffic being diverted through China and European mobile phone traffic briefly rerouted through Chinese servers. These incidents align with HNDL strategies and emphasize the need for stronger encryption.
"Harvest Now, Decrypt Later is at the heart of signals intelligence. There are vast tape libraries at NSA… running back decades." – Whitfield Diffie, Cryptographer
The economics of data harvesting make it even more appealing. Digital storage costs have dropped by 95% since 2010, making it affordable for nation-states to maintain massive archives of encrypted data. Once harvested, this data remains vulnerable indefinitely. This is especially concerning for information that needs long-term protection, such as intellectual property, health records, financial data, and trade secrets – data that must stay secure for 10 to 25+ years.
Experts estimate a 5% to 14% chance of a cryptographically relevant quantum computer being developed by 2029, with that probability increasing to 34% within the next decade. If your data needs to remain secure beyond that timeframe, the time to act is now.
What Makes Quantum-Resistant Encryption Secure
Post-Quantum Cryptography Algorithms
Traditional encryption methods like RSA and ECC rely on mathematical problems – such as integer factorization and discrete logarithms – that quantum computers can solve efficiently. Post-quantum cryptography (PQC), on the other hand, is based on problems that remain computationally hard even for quantum computers. These algorithms are designed to work on today’s hardware, making them ready for immediate use.
In August 2024, NIST finalized the first three PQC standards. ML-KEM (formerly CRYSTALS-Kyber) is the primary standard for encryption and key establishment. It uses lattice-based cryptography, specifically the Learning-with-Errors (LWE) problem, which involves finding short vectors in high-dimensional lattices – a task quantum computers find extremely difficult. ML-KEM offers moderate key sizes, such as Kyber-768’s ~1,184-byte public key, and has already been integrated into major platforms like Microsoft’s SymCrypt library, enabling quantum-resistant encryption on Windows and Azure.
ML-DSA (formerly CRYSTALS-Dilithium) is used for generating digital signatures. It employs a "Fiat-Shamir with aborts" method, producing signatures (~2,420 bytes for Dilithium2) that are larger than ECDSA’s 64 bytes but provide quantum resistance. In August 2024, Google Cloud KMS introduced preview support for ML-DSA, allowing users to generate quantum-resistant signatures for cloud-based data.
SLH-DSA (formerly SPHINCS+) is a backup signature scheme based on hash-based cryptography. Its security depends entirely on one-way hash functions. While SPHINCS+ offers robust protection, it requires larger signature sizes (7,856 to 17,088 bytes). Additionally, in March 2025, NIST selected HQC (Hamming Quasi-Cyclic) as a code-based alternative for key encapsulation.
"There is no need to wait for future standards. Go ahead and start using these three… for most applications, these new standards are the main event." – Dustin Moody, Head of NIST PQC Standardization Project
| Feature | Classical (RSA/ECC) | Post-Quantum (ML-KEM/ML-DSA) |
|---|---|---|
| Hard Problem | Factoring / Discrete Log | Lattices / Hash Functions |
| Quantum Resistance | Vulnerable to Shor’s Algorithm | Resistant to known quantum attacks |
| Key/Signature Size | Very Small (bytes) | Moderate to Large (kilobytes) |
These quantum-resistant algorithms are designed to secure key exchanges and digital signatures. Meanwhile, symmetric encryption methods like AES-256 remain reliable when paired with quantum-safe key exchange mechanisms.
Why AES-256 Still Works
While post-quantum cryptography focuses on asymmetric encryption, symmetric encryption methods like AES-256 remain highly secure. When combined with quantum-safe key exchanges, AES-256 provides a robust layer of protection.
AES-256 is a symmetric encryption algorithm, meaning it uses the same key for both encryption and decryption. Unlike public-key systems, symmetric encryption isn’t vulnerable to Shor’s algorithm. While Grover’s algorithm can speed up attacks on symmetric encryption, it only reduces the effective key strength by half. This means AES-256, which offers 256-bit security in classical terms, still provides 128 bits of security in a quantum context – making it computationally infeasible to break.
However, the key exchange protocols traditionally used with AES-256, such as RSA or ECDH, are vulnerable to quantum attacks. To address this, organizations are adopting hybrid encryption models that combine classical methods with post-quantum algorithms. For instance, Cloudflare implemented a hybrid key exchange that uses X25519 alongside ML-KEM to securely establish AES-256 keys, ensuring both the key exchange and the encrypted data are protected.
"AES-256 itself is considered quantum-resistant for symmetric encryption. However, the key exchange mechanism that establishes AES keys typically uses RSA or ECDH, which are quantum-vulnerable. You need quantum-safe key exchange (like ML-KEM) combined with AES to achieve full quantum-safe encryption." – QRAMM
For those still using AES-128, transitioning to AES-256 is a smart move to ensure at least 128-bit security against potential quantum threats.
How to Implement Quantum-Resistant Encryption
Step 1: Inventory Your Cryptographic Systems
Start by taking stock of all systems in your organization that use encryption. This includes VPNs, TLS setups, IoT devices, and even third-party libraries. A Cryptographic Bill of Materials (CBOM) can help you map out all dependencies effectively. Pay close attention to systems relying on vulnerable public-key encryption methods like RSA, Diffie-Hellman, and ECC, and identify those already using quantum-resistant options such as AES-256 or SHA-256.
Consider the longevity of your data. If sensitive information needs protection for 5 to 25 years – or if systems like industrial controls, satellites, or medical devices are expected to operate for decades – these may need hardware updates to handle the larger key sizes required for post-quantum cryptography.
Use tools like the MITRE PQC Inventory Workbook or the PKIC PQC Capabilities Matrix to organize your findings. Focus on "High Value Assets" and "High Impact Systems" using established government standards. Apply Mosca’s Theorem to assess urgency: if the time it takes to break your encryption plus the time needed to retool your systems exceeds the lifespan of the data’s security needs, you’re already behind.
"If the time to break your crypto (with a quantum computer) plus the time to retool your systems exceeds the time those systems need to remain secure, then you’re already late." – Michele Mosca, Cryptographer
With your inventory complete, you’ll be ready to transition to NIST-approved post-quantum algorithms.
Step 2: Switch to Quantum-Resistant Algorithms
Once your inventory is done, the next step is migrating to NIST-approved post-quantum algorithms. Current standards include FIPS 203 (ML-KEM), FIPS 204 (ML-DSA), and FIPS 205 (SLH-DSA). Start with a hybrid approach by combining classical algorithms like X25519 with post-quantum ones. This dual-layered strategy ensures that if a post-quantum algorithm becomes vulnerable, the classical layer still offers protection.
For TLS connections, implement hybrid key exchanges using RFC 9370 standards. If your VPNs rely on IKEv2, adopt RFC 8784 with Post-Quantum Pre-Shared Keys (PPKs). Ensure these PPKs have at least 256 bits of entropy, which corresponds to 128 bits of post-quantum security at NIST Category 5. Build flexibility into your systems by making algorithm selection configurable rather than hardcoded.
Plan your migration based on risk levels:
- Critical systems (e.g., those handling classified data or long-lived secrets) should transition within 12 months.
- High-priority systems (e.g., those involving sensitive PII) can follow within 12 to 24 months.
- Internal applications may have a longer timeline of 24 to 48 months.
- Systems with short-lived encryption needs may wait 48+ months.
Step 3: Upgrade Key Management Systems
Your key management infrastructure must be capable of handling the larger key sizes and higher computational demands of quantum-resistant algorithms. This often means upgrading or replacing Hardware Security Modules (HSMs). Many existing HSMs may require firmware updates or even complete replacements to support post-quantum cryptographic operations.
Start conversations early with your HSM vendors to understand their timelines for supporting NIST-approved PQC algorithms. During this transition, ensure encrypted data headers include algorithm identifiers for backward compatibility.
Step 4: Test Before Full Deployment
Before rolling out quantum-resistant encryption enterprise-wide, conduct pilot projects on critical systems. These tests should:
- Confirm compatibility across different vendors and platforms.
- Measure performance impacts on latency and throughput.
- Include side-channel audits and timing analyses to identify vulnerabilities.
Expect performance changes. For instance, adding Level 3 PQC to IKEv2 key exchanges may increase latency by 20 to 30 milliseconds, while Level 5 could add 40 to 60 milliseconds. Stronger schemes like Classic McEliece might add over 800 milliseconds, potentially causing fragmentation. Test these impacts thoroughly on your network, storage, and CPU resources.
When testing VPNs, use "Mandatory" negotiation modes to ensure connections fail if quantum resistance isn’t established. This helps mitigate "Harvest Now, Decrypt Later" attacks. Work closely with peer administrators to align on PQC parameters and conduct regular migration drills to refine your processes.
Once pilot tests are successful, you can finalize deployment and keep systems updated.
Step 5: Stay Updated on Standards
After inventorying, migrating, and testing, staying informed about evolving quantum-resistant standards is critical. For example:
- The U.S. federal government requires quantum-safe encryption by 2035.
- The European Union has set 2030 as the deadline for critical industries like finance.
- The U.K. National Cyber Security Centre has milestones for 2028.
To stay compliant, partner with hosting providers offering quantum-safe SSL certificates, such as Serverion, which provides SSL certificates and server management across global data centers. Keep your systems adaptable – large-scale cryptographic migrations often take 5 to 10 years, so starting early is key.
Benefits of Quantum-Resistant Encryption
Protection Against Future Quantum Attacks
Switching to quantum-resistant encryption today is a proactive way to shield your enterprise from "Harvest Now, Decrypt Later" (HNDL) attacks. These attacks involve intercepting and storing data now, with the intent to decrypt it in the future using quantum computing. Sensitive information like intellectual property, medical records, and confidential business communications could already be at risk, sitting in storage, waiting for quantum capabilities to catch up.
This step is especially important for data that needs to remain confidential for decades – think R&D files, legal contracts, or patient health records. By transitioning to NIST-approved algorithms such as FIPS 203 (ML-KEM) and FIPS 204 (ML-DSA), along with upgrading to AES-256, you can ensure your data stays secure even when cryptographically relevant quantum computers (CRQCs) become a reality.
Quantum-resistant algorithms also protect digital signatures and Public Key Infrastructure (PKI) from future threats. This stops attackers from forging certificates, impersonating trusted entities, or injecting malicious software updates. Essentially, your entire trust chain – from device authentication to firmware updates – remains secure.
And it’s not just about protecting data. These measures also strengthen your organization’s reputation and credibility.
Improved Customer Trust and Regulatory Compliance
Beyond addressing technical threats, adopting quantum-resistant encryption provides broader business advantages. One of the biggest benefits? Increased customer trust. When you show that you’re ahead of the curve in securing against emerging risks, clients feel confident that their sensitive information is safe. This can set you apart in industries like finance, healthcare, and telecommunications, where data security and retention are critical.
Regulations are also tightening. The U.S. Quantum Computing Cybersecurity Preparedness Act and NIST’s plan to phase out quantum-vulnerable algorithms by 2035 signal clear deadlines. In the UK, the National Cyber Security Centre has recommended that high-risk systems migrate by 2030, with full adoption required by 2035. Similarly, the European Union has set 2030 as a deadline for critical industries to make the switch. By adopting quantum-resistant measures now, you’ll avoid the last-minute rush to meet these requirements and the potential costs of non-compliance.
"Preparing for quantum threats isn’t just about safeguarding data – it’s about future-proofing trust in a digital world that’s evolving faster than ever before." – PwC Middle East
Another key advantage is crypto-agility – the ability to update or swap out algorithms without overhauling your systems. This flexibility ensures you can adapt to future vulnerabilities without major disruptions. Partnering with providers like Serverion, which specializes in different types of SSL certificates and server management globally, can help keep your infrastructure compliant and ready for quantum-era challenges.
These reasons highlight why early adoption of quantum-resistant encryption is not just a smart move – it’s a necessary one.
Conclusion
Key Takeaways
The need for quantum-resistant encryption isn’t a far-off concern – it’s a pressing issue for enterprises right now. Why? Because attackers are already intercepting sensitive data, planning to decrypt it once quantum computers become powerful enough. Considering that large-scale cryptographic migrations can take 5 to 10 years, waiting until 2030 to act could leave you dangerously behind.
Here’s a practical plan to prepare: start by inventorying your systems, then implement NIST-approved post-quantum algorithms like ML-KEM or ML-DSA. Upgrade your key management systems to handle larger keys, run pilot tests to iron out deployment issues, and keep a close eye on evolving standards. And don’t overlook an immediate upgrade to AES-256, which offers about 128-bit post-quantum security against Grover’s algorithm.
From a financial perspective, acting now makes sense. For organizations with a $1 billion IT budget, transitioning today might cost around $25 million. But delaying until 2035 could double that expense. Regulatory deadlines add urgency too – U.S. federal agencies must comply by 2035, while critical sectors in the EU face a 2030 deadline.
The benefits go beyond compliance and cost savings. Quantum-resistant encryption strengthens customer trust, ensures regulatory compliance, and builds crypto-agility for adapting to future algorithm changes. To navigate this complex shift, consider working with experienced providers like Serverion, known for its SSL certificates and server management services across global data centers.
"If the time to break your crypto plus the time to retool your systems exceeds the time those systems need to remain secure, then you’re already late." – Michele Mosca, Cryptographer
FAQs
Which of our data is most at risk from ‘harvest now, decrypt later’ attacks?
Sensitive information that requires long-term protection – like state secrets, health records, classified government communications, legal contracts, and financial data – is particularly vulnerable. Such data could be intercepted and stored today, only to be decrypted later when quantum computers gain the power to crack current encryption methods.
How can ML-KEM and ML-DSA be added without disrupting existing TLS, VPN, or PKI setups?
To incorporate ML-KEM and ML-DSA into existing TLS, VPN, or PKI systems without causing disruptions, hybrid or composite schemes are the way to go. These schemes merge post-quantum algorithms with traditional ones like RSA or ECDHE. This combination ensures compatibility with current setups while allowing a gradual transition. It also provides a fallback to classical algorithms, ensuring security and smooth integration. This method lets post-quantum solutions coexist with established protocols, maintaining backward compatibility during testing and deployment.
What performance and hardware changes should we expect with post-quantum keys and signatures?
Post-quantum certificates are significantly larger – roughly 10 to 15 times the size of traditional certificates. This increase means they use more bandwidth during TLS handshakes, which could lead to added latency, especially on networks that already experience high delays. On top of that, quantum-resistant algorithms, such as Kyber and Dilithium, demand more computational power. This could result in the need for hardware upgrades or optimizations to manage the extra processing load while still meeting performance goals and maintaining service level objectives (SLOs).







